Product Introduction
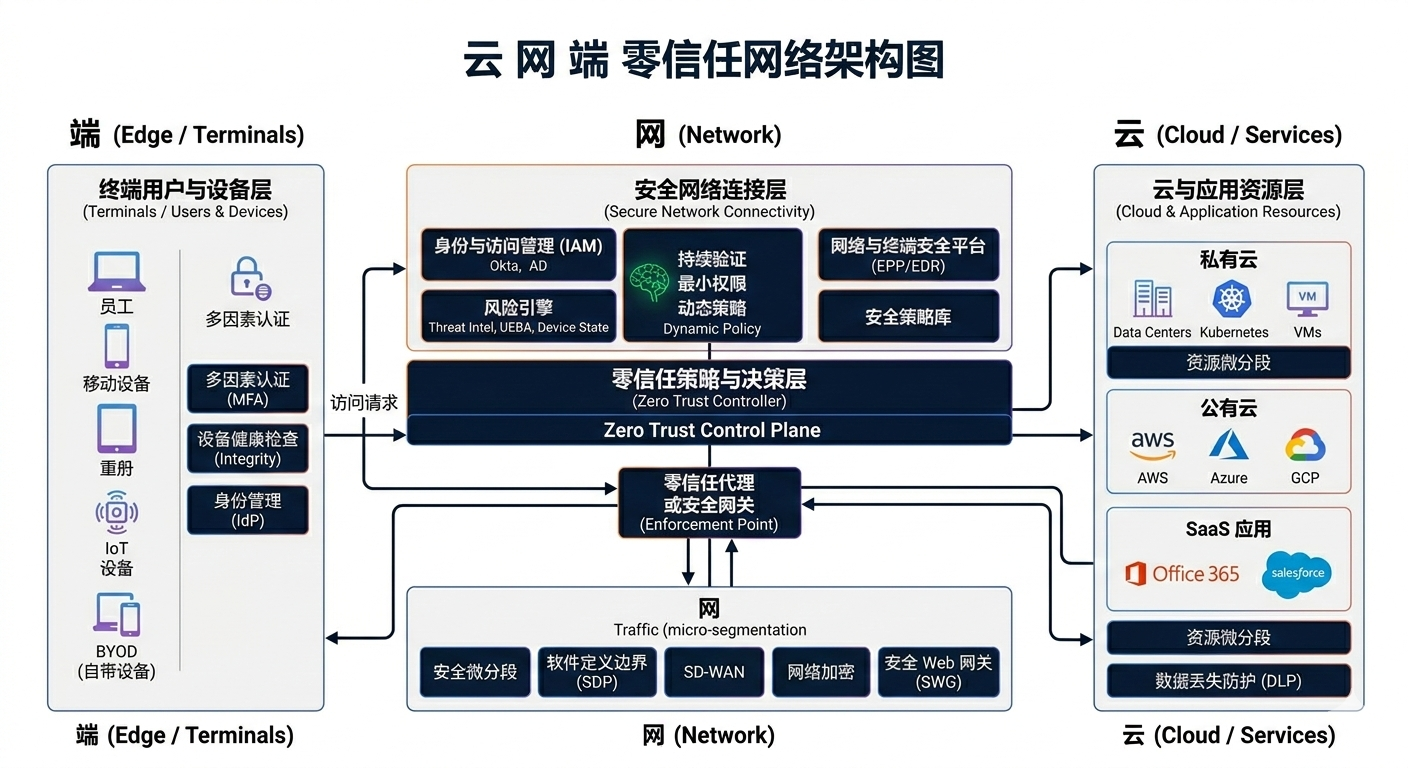
Zero Trust Network Access (ZTNA) is a security policy designed to prevent unauthorized access and protect an organization's internal network. Its core principle is "Never Trust, Always Authenticate," meaning that authentication and authorization are mandatory for access to network resources, regardless of the user, device, or network location. This policy helps prevent potential cyberattacks and data breaches.
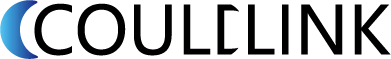
A centrally managed and secure "cloud" + a globally accelerated "network" + a unified "terminal" with comprehensive security capabilities.
Product Features
Asset stealth reduces attack surface
By consolidating enterprise assets onto a platform, the amount of IP addresses, ports, and other information exposed to the outside world is reduced, thereby minimizing the attack surface.
Minimum Access Control
Develop fine-grained access permissions based on personnel and application dimensions to achieve minimum access permissions for enterprise employees.
Supports multiple authentication methods
In addition to verifying account passwords, it also supports further authentication of employee identities through methods such as dynamic passwords on the App, email verification codes, and SMS verification codes.
Without changing user access habits
With a single agent or no agent, employees can seamlessly switch between internal and external networks, improving their work efficiency and access experience.
Continuous monitoring of users and devices
Whether accessing the intranet or the internet, user devices and user behavior are continuously monitored to achieve comprehensive auditing and prevent legal risks.
Real-time feedback allows for flexible strategy adjustments
Employees' access to the intranet is reported to the console in real time. Administrators can adjust policies gradually based on the access logs to meet access needs.
Service Scenarios
Design flexible, meet the needs of different network scenarios for enterprises
Solution
- Multi-dimensional access control by identity, device, location, context and app
- Client connects to nearest global acceleration node
- Mesh network, auto-routing, no VPN or dial-up; access authorized apps across any datacenter
- TLS reverse gateway keeps internal apps hidden from the internet
- URL/API-level access control and audit logs
Solution advantages
- Identity- and app-based access control; least privilege, no lateral movement, full visibility
- Near-edge global acceleration for better performance
- Mesh: scalable, highly available, disaster-resistant
- Single client for multi-datacenter apps, better UX
- Internal apps hidden from the internet
- One client integrates DLP, EDR and more
Customer Value
 Lower CostOne SASE for office security; low deployment and zero ops overhead.
Lower CostOne SASE for office security; low deployment and zero ops overhead. Higher EfficiencyGo live in 15 minutes; branch onboarding in minutes.
Higher EfficiencyGo live in 15 minutes; branch onboarding in minutes. Stronger SecuritySame security for HQ, branch, WFH, and mobile.
Stronger SecuritySame security for HQ, branch, WFH, and mobile. Better ExperienceUnified secure client, no lag; near-edge access for smooth visits; SSO in trusted env; auto-connect for seamless remote work.
Better ExperienceUnified secure client, no lag; near-edge access for smooth visits; SSO in trusted env; auto-connect for seamless remote work.
Understanding Zero Trust Secure Access
- SAAS Global Acceleration
- Global Enterprise Network
- Retail Chains
Industry Solutions
- Introduction to CouldLink
About Us
Contact us

Scan and follow our WeChat official account